The operational technology security market is estimated to be valued at USD 22,588.9 Mn in 2026 and is expected to reach USD 40,504.5 Mn by 2033, exhibiting a compound annual growth rate (CAGR) of 8.7% from 2026 to 2033.
The operational technology security market is experiencing steady growth, primarily fueled by the increasing frequency and sophistication of cyber threats targeting industrial control systems and critical infrastructure. As industries adopt IoT, automation, and cloud-based solutions, the attack surface for cybercriminals is expanding, which is driving higher operational technology security market demand across manufacturing, energy, and transportation sectors.
|
Current Events |
Description and its impact |
|
Rising Cyber-attacks on Critical Infrastructure |
|
|
Government Regulations and Compliance Mandates |
|
|
Integration of AI and Machine Learning in OT Security |
|
Uncover macros and micros vetted on 75+ parameters: Get instant access to report
Artificial Intelligence (AI) and Machine Learning (ML) are also reshaping operational technology security by enhancing predictive threat detection, automating incident response, and reducing false positives. Vendors are increasingly embedding AI-driven analytics into their platforms, enabling faster and smarter defence mechanisms. Overall, anomaly detection and intrusion prevention lead adoption, while AI, ML, and Zero Trust represent the fastest-growing technologies shaping the future of OT security.
For instance, in August 2025, Frenos, a specialist in AI-native operational technology (OT) security, partnered with N2K Networks to unveil SAIRA, an OT security posture management platform powered by certified, industry-validated intelligence. Unlike traditional systems relying on generic AI, SAIRA leverages N2K’s professional certification dataset, covering more than 100 credentials and refined over 25 years to deliver expert-level reasoning in vulnerability identification and response.
By industry, the power generation & electrical segment led with a 27.8% share in 2026, driven by increasing adoption of smart grids, digital monitoring, and the need to secure electrical assets from cyber intrusions. Investments in renewable energy and intelligent power systems further accelerate demand for robust OT security frameworks.
In April 2026, Spain’s National Cybersecurity Institute (Incibe) investigated small electricity generators, including solar and wind farms, following a nationwide blackout affecting 50 million people in Spain and Portugal. Authorities examined whether vulnerabilities in these smaller facilities could have been exploited to disrupt the power grid. Over the past year, Spain reported 100,000 cyberattacks, with 70% targeting businesses and organizations, prompting a €1.1 billion investment to enhance national cybersecurity.
To learn more about this report, Request Free Sample
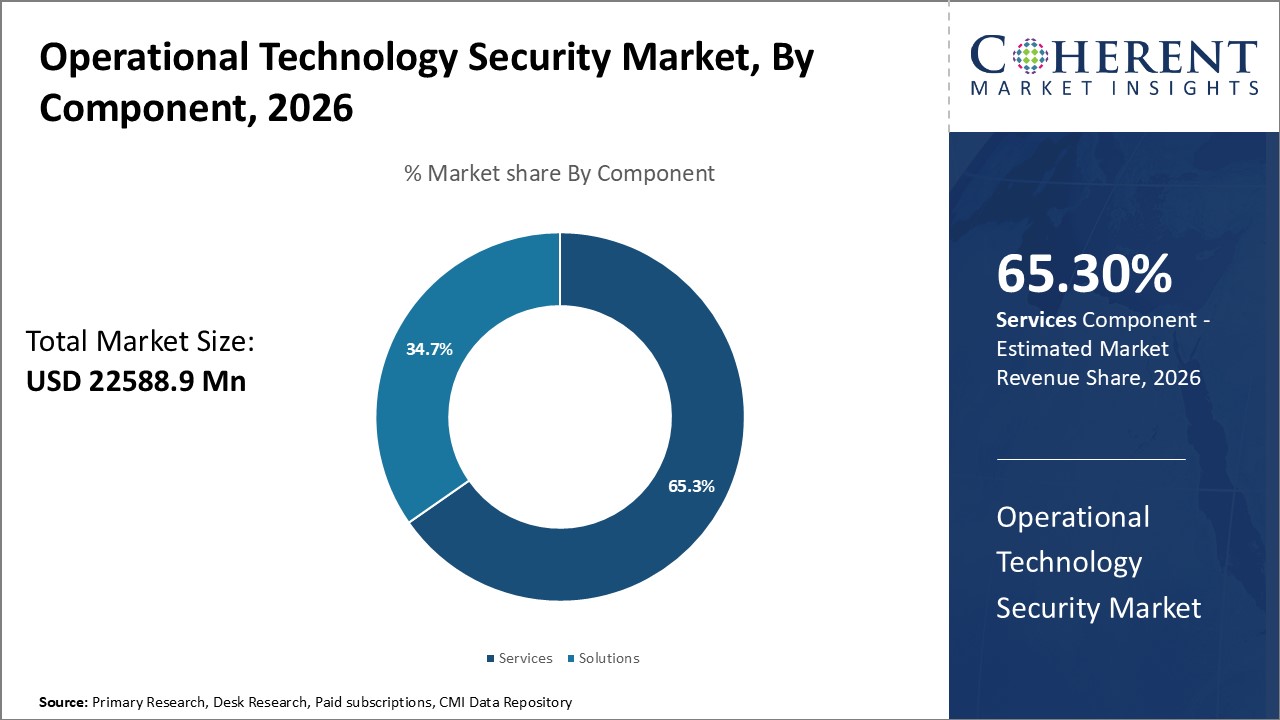
Based on component, the services segment accounted for 65.3% of the market share in 2026, driven by the increasing reliance on managed security services, consulting expertise, and tailored solutions for critical infrastructure protection. Enterprises are increasingly outsourcing to specialized providers for real-time monitoring, incident response, and compliance management. The dominance of this segment reflects the growing complexity of OT environments and the need for continuous threat intelligence and proactive risk mitigation strategies.
In August 2025, SonicWall announced the launch of its new Managed Security Services Division, appointing channel and industry veteran Michael Crean as General Manager. This move represents a pivotal step in SonicWall’s transition from a product-centric vendor to a full-service cyber security partner for Managed Service Providers (MSPs) and Managed Security Service Providers (MSSPs).
To learn more about this report, Request Free Sample
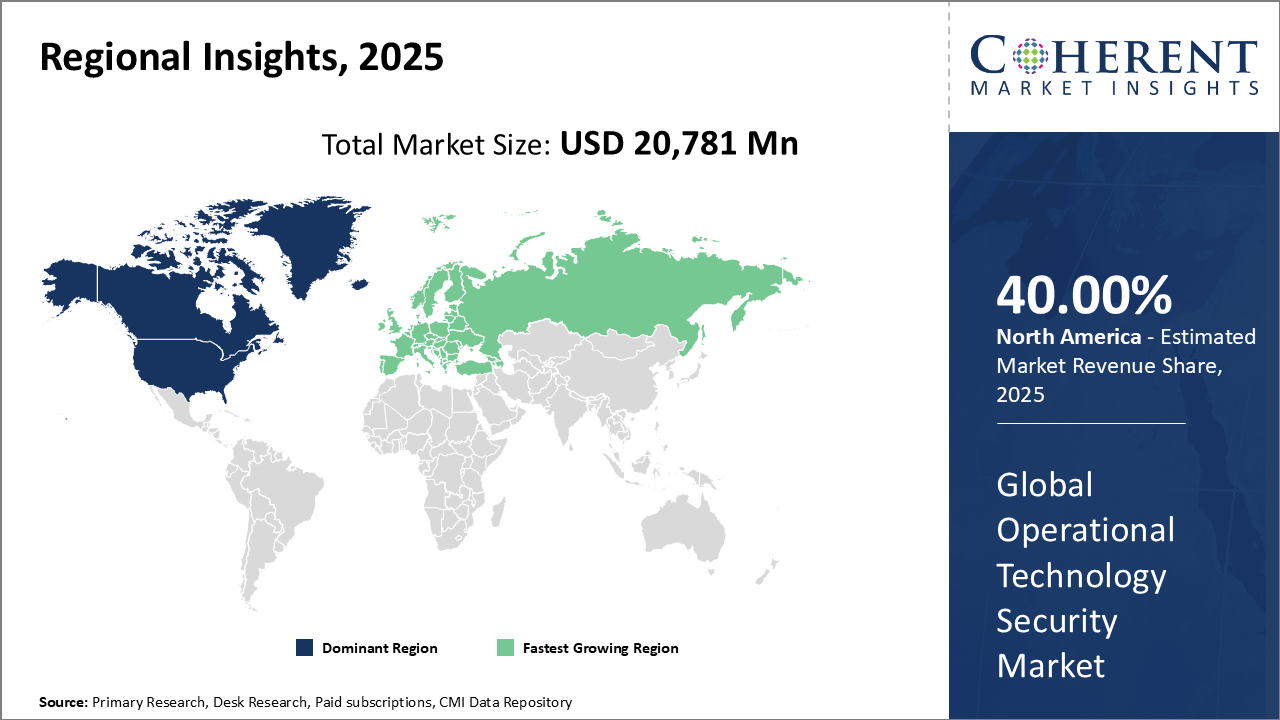
North America is expected to dominate the global operational technology security market with a 40.00% share in 2026, led by strong cyber security regulations, advanced infrastructure, and robust investments in industrial security. The United States is at the forefront, driven by initiatives such as CISA’s critical infrastructure protection programs and rising OT security adoption across energy, manufacturing, and utilities sectors. Canada is also witnessing steady growth, supported by increasing digitalization in oil & gas, mining, and power generation, creating opportunities for security vendors and solution providers.
In July 2026, Trustwave, a global cybersecurity and managed security services leader, announced the launch of its advanced Operational Technology (OT) services portfolio, aimed at strengthening the defense of critical infrastructure and industrial operations against evolving cyber threats. Building on decades of research, innovation, and threat intelligence from its renowned SpiderLabs team, the new services position Trustwave as a preferred partner for organizations navigating the convergence of IT and OT.
Europe is projected to hold a 26.0% share in 2026, supported by strict data protection policies, Industry 4.0 adoption, and strong emphasis on industrial resilience. Germany, the UK, and France are leading in OT cyber security adoption due to their advanced manufacturing bases and regulatory frameworks like GDPR and NIS2 Directive. Growing adoption of automation in automotive, aerospace, and energy industries continues to drive demand for advanced OT security solutions across the region. In March 2026, Integrity360, a leading cyber security firm, acquired Holiseum, a Paris-based company specializing in OT and IoT security. This acquisition enhances Integrity360's capabilities in securing critical infrastructure across Europe, particularly in France.
The United States holds a dominant position in the North American operational technology security market, commanding a 31% share in 2026. Its leadership is driven by stringent cyber security regulations, advanced industrial infrastructure, and substantial investments in safeguarding critical assets. Programs such as CISA’s critical infrastructure protection initiatives, along with widespread OT security adoption across the energy, manufacturing, and utilities sectors, have reinforced the U.S.’s role as a regional and global trendsetter, promoting innovation, advanced security solutions, and active vendor participation.
In June 2026, the U.S. National Institute of Standards and Technology (NIST) emphasized the increasing convergence of operational technology (OT) and information technology (IT), driven by the rise of IoT and internet-connected equipment that were once isolated. The agency noted that OT systems including industrial control systems, building automation, and transportation networks are connecting to broader networks, introducing new cyber security challenges for organizations.
The United Kingdom demand is observed in the European operational technology security market, commanding a 7% share in 2026. Its prominence is supported by strict data protection policies, strong Industry 4.0 adoption, and an emphasis on industrial resilience. Widespread OT security implementation across manufacturing, energy, and critical infrastructure sectors, combined with regulatory frameworks such as GDPR and the NIS2 Directive, reinforces the U.K.’s role as a key player in shaping regional OT security trends, driving innovation, and fostering robust vendor management.
For instance, in August 2026, the UK government has pledged £1 billion in funding to enhance cybersecurity for Operational Technology (OT) systems which are critical infrastructure operating often offline. The investment underscores the importance of identity-centric OT security, which ensures every user and session is authenticated through dynamic, time-limited access controls, even without network connectivity.
| Report Coverage | Details | ||
|---|---|---|---|
| Base Year: | 2025 | Market Size in 2026: | USD 22,588.9 Mn |
| Historical Data for: | 2020 To 2024 | Forecast Period: | 2026 To 2033 |
| Forecast Period 2026 to 2033 CAGR: | 8.7% | 2033 Value Projection: | USD 40,504.5 Mn |
| Geographies covered: |
|
||
| Segments covered: |
|
||
| Companies covered: |
Accenture plc, Belden Inc., Cisco Systems, Inc., Claroty Ltd., CyberX, Cyberbit, and Darktrace |
||
| Growth Drivers: |
|
||
| Restraints & Challenges: |
|
||
Uncover macros and micros vetted on 75+ parameters: Get instant access to report
As operational technology networks continue to become increasingly connected to enterprise IT infrastructures and public networks like the internet, they have grown more vulnerable to cyber-attacks. The traditional air gaps that once separated these systems are disappearing as organizations look to leverage connectivity and data insights across departments. But bringing OT online also exposes critical infrastructure systems controlling everything from energy generation to water treatment to new threat vectors. Recent incidents involving ransom ware like the attack on Colonial Pipeline have underscored the risks of unsecured OT environments.
Regulators and asset owners alike are recognizing that strong security is imperative for these networked control systems that underpin essential public services and national infrastructure. The demand is therefore growing for solutions that can help OT stakeholders implement proper governance, segmentation, access control, and monitoring of their operational networks. Vendors offering industrial cyber security technology and services are well positioned to benefit from this driver are poised to strengthen their position and expand their operational technology security market share in the coming years.
The operational technology security market is undergoing a structural shift, driven less by compliance mandates and more by existential threats to industrial continuity. Traditional perimeter-based approaches are proving inadequate as industrial control systems (ICS) and supervisory control and data acquisition (SCADA) platforms become increasingly interconnected with IT networks. The consequence is a rise in high-impact cyberattacks. According to Dragos, over 70% of ransomware incidents in critical infrastructure during 2023 targeted operational environments, highlighting the urgency for proactive defense.
One critical observation is that market adoption is being dictated not by availability of solutions, but by trust in vendors. Industrial enterprises are reluctant to engage with IT-first cybersecurity providers who lack domain-specific expertise in automation, power grids, or oilfield technologies. This trust gap is narrowing only where vendors demonstrate incident response experience in high-stakes OT environments. For instance, Schneider Electric’s Zero Trust OT initiative and Siemens’ integration of OT-specific intrusion detection have found traction precisely because they speak the language of industrial engineers, not just CISOs.
Another key shift is that the operational technology security market value is increasingly tied to prevention of downtime rather than regulatory penalties. In the oil & gas industry, an hour of production halt at an offshore rig can cost upwards of USD 300,000–500,000. When benchmarked against such figures, the operational technology security market price for advanced anomaly detection or AI-driven monitoring solutions appears comparatively negligible. In this sense, pricing is less about software cost and more about the value of uninterrupted operations.
Share
Share
Ankur Rai is a Research Consultant with over 5 years of experience in handling consulting and syndicated reports across diverse sectors. He manages consulting and market research projects centered on go-to-market strategy, opportunity analysis, competitive landscape, and market size estimation and forecasting. He also advises clients on identifying and targeting absolute opportunities to penetrate untapped markets.
Joining thousands of companies around the world committed to making the Excellent Business Solutions.
View All Our Clients