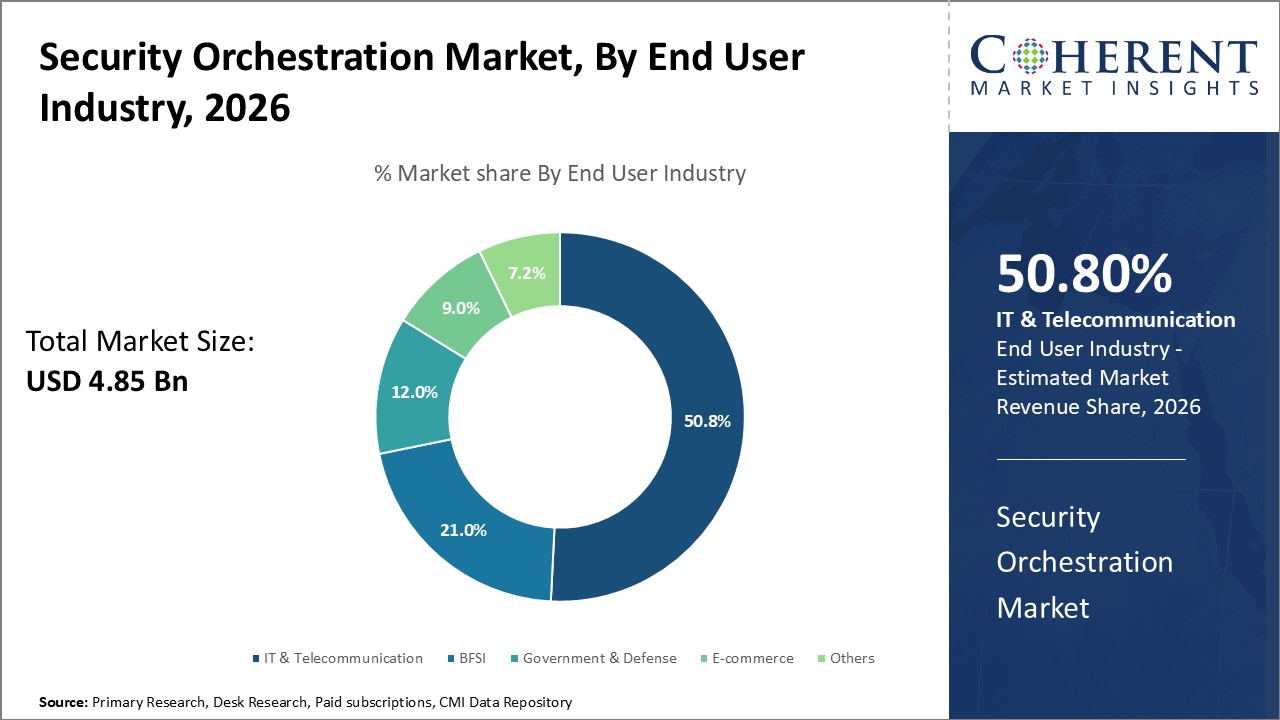
Global security orchestration market is estimated to be valued at USD 4.85 Bn in 2026 and is expected to reach USD 13.55 Bn by 2033, exhibiting a compound annual growth rate (CAGR) of 15.8% from 2026 to 2033.
To learn more about this report, Request Free Sample
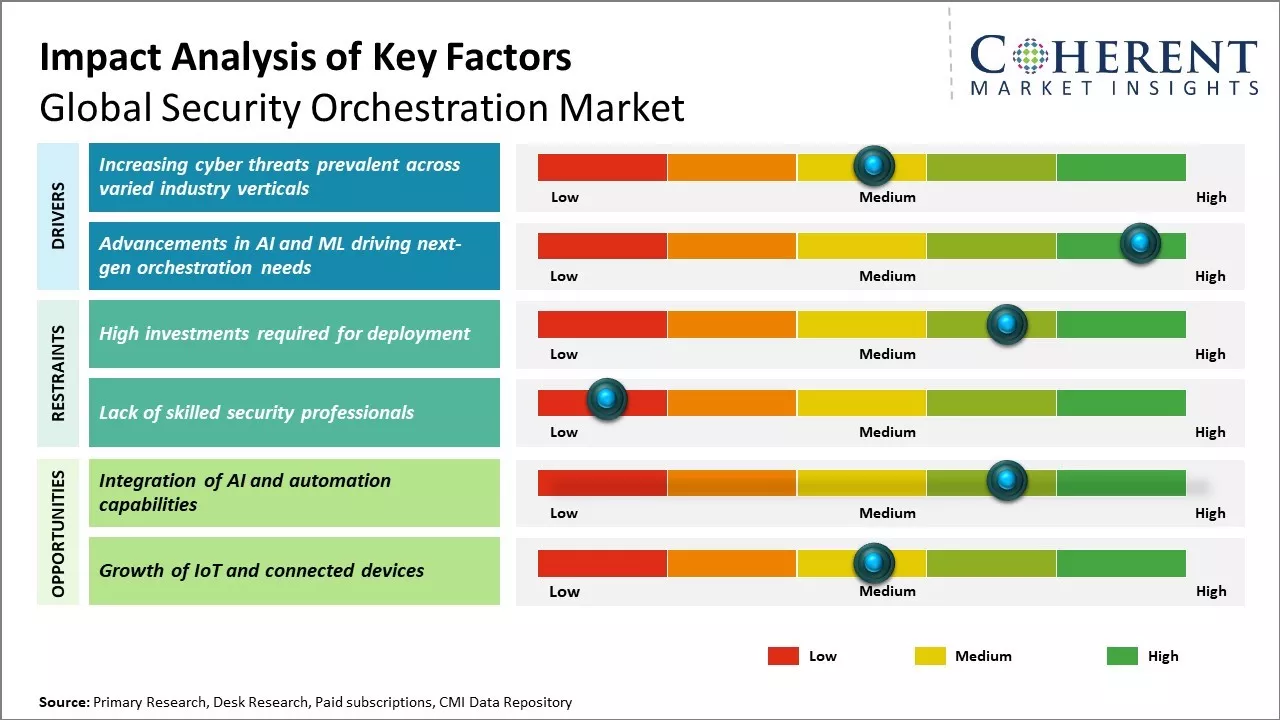
Increasing cyberattacks and rising demand for centralized security operations is driving the security orchestration market growth. Furthermore, rising need to automate security operations and integrate it with existing security infrastructure can boost adoption of security orchestration. Emerging technologies like artificial intelligence and machine learning are helping vendors develop more sophisticated security orchestration solutions. Integration of security orchestration platforms with IT service management solutions is a key trend in the market. Adoption across sectors like BFSI, government, and healthcare can drive the market growth during the forecast period. However, high initial investment and complexity of deployment and management of security orchestration solutions can hamper the market growth.
|
Current Event |
Description and its Impact |
|
Artificial Intelligence and Machine Learning Integration Boom |
|
|
Economic Pressures and IT Budget Optimization |
|
Uncover macros and micros vetted on 75+ parameters: Get instant access to report
The security orchestration, automation, and response (SOAR) market is experiencing a revolutionary transformation as artificial intelligence becomes deeply integrated into cybersecurity frameworks. Organizations worldwide are leveraging AI to enhance threat detection, streamline incident response, and create more resilient security postures against increasingly sophisticated cyber threats.
In September 2025, Pax Intelligence made its official debut with the launch of the industry's first Security Orchestration, Automation, and Premediation (SOAP) platform. Designed to move past conventional reactive security measures, the platform uses predictive AI to actively anticipate and stop cyber threats before they occur.
Evolving cyber landscape along with changing nature of threats has pushed organizations across all industry verticals to bolster their security posture. There has been increase in ransomware attacks, phishing campaigns, malware intrusions and other advanced cyber-attacks, causing monetary losses as well as damaged reputation.
While large enterprises have been traditionally investing sizable amounts in security, mid-market and small organizations are also recognizing the business-critical need for integrating robust defense solutions. Traditional siloed point security products are unable to provide the requisite threat visibility and coordinated response capabilities needed to detect and remediate multi-staged complex attacks.
There has been growing understanding among CISOs and security leaders that centralized security orchestration, automation and response play a pivotal role in weaving various infrastructure components together to detect threats across environments in a more cohesive manner. This allows enterprises to establish situational awareness, prioritize incidents based on criticality and threat level while ensuring fast and streamlined remediation actions. The continuously evolving nature of cyber risks has made security orchestration an imperative for enterprises aiming to stay ahead of cybercriminals.
By offering, software segment is estimated to contribute the highest market share of 63.9% in 2026, due to increasing adoption of advanced threat protection solutions by organizations across various industries. As cyber-attacks become more sophisticated, businesses are focusing on implementing security orchestration software that offer automated detection and response capabilities.
Software provides a centralized interface for security administrators to monitor threats across different security tools and coordinate response actions in real-time. This saves valuable time for security teams and improves their efficiency in mitigating damage from security breaches.
Security orchestration software helps consolidate security processes on a single platform, eliminating the need to navigate through multiple consoles. This streamlines security operations and allows enterprises to achieve enhanced visibility and control over their dispersed IT infrastructure.
In May 2025, ServiceNow introduced AI agents within its Security and Risk solutions, marking a new phase in enterprise security. These agents enhance consistency, deliver insights, and speed up response times, supporting the move toward self-defending enterprises. In partnership with Microsoft and Cisco, ServiceNow aims to shift security from reactive defense to autonomous resilience with expanded, ethical, and efficient capabilities. Such developments are proliferating the security orchestration market share.
To learn more about this report, Request Free Sample
By end user industry, IT and telecommunication segment is estimated to contribute the highest market share of 50.8% in 2026, due to growing need for advanced security orchestration solutions across their complex networks that span different geographies. As digital transformation initiatives gather pace in the IT and telecom sector, the attack surface for cybercriminals also widen.
Traditional security tools are unable to provide adequate protection due to dynamic nature of IT infrastructure in this industry. This has boosted investments in automated security orchestration platforms tailored for managing security policies and response measures across hybrid IT environments.
The integration of security orchestration with existing security investments further enhances visibility and control for IT and security teams in these organizations. It helps streamline compliance tasks, prioritize threats based on business criticality, minimize security blind spots and reduce dwell time during breaches.
With 5G rollouts and proliferation of IoT/OT devices, the need for cross-domain threat visibility and coordination becomes even more crucial for maintaining business continuity. The IT and telecom sector's early adoption of advanced security orchestration solutions can revolutionize security operations management for this industry.
For instance, in April 2023, D3 Security released Smart SOAR, a new version of its security orchestration, automation and response solution.
To learn more about this report, Request Free Sample
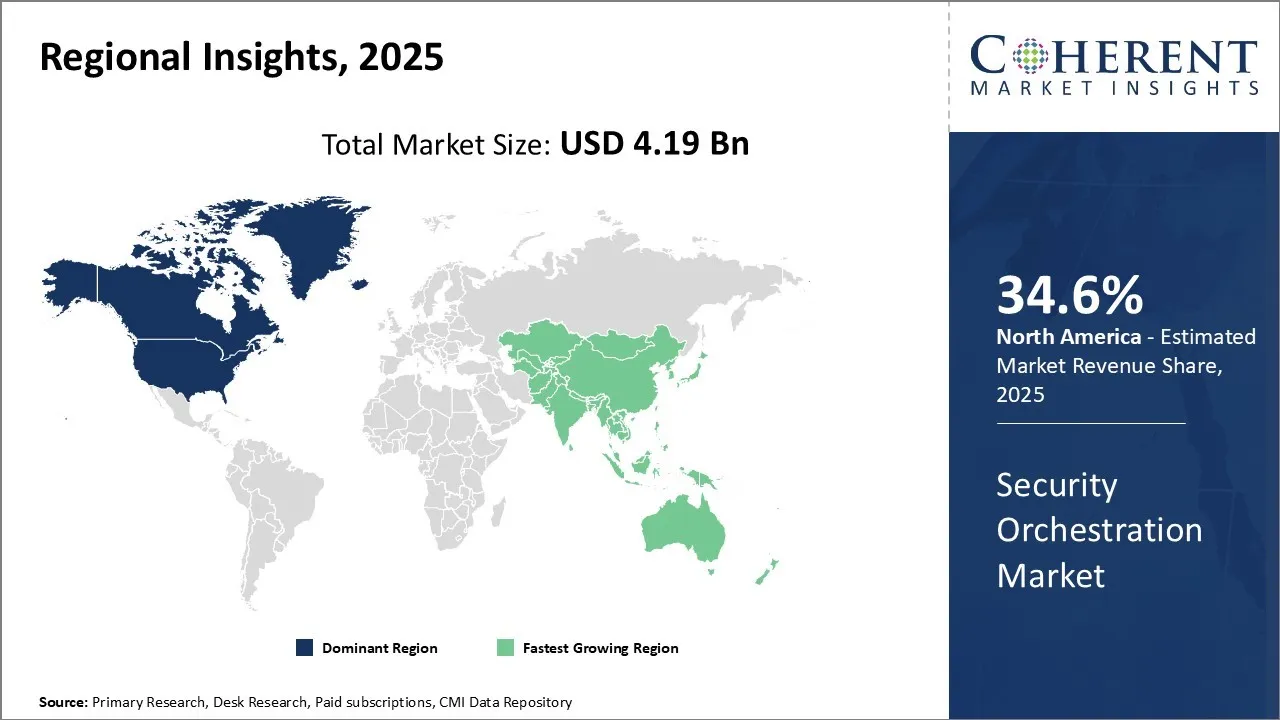
North America dominates the security orchestration market, with an estimated market share of 34.6% in 2026. This can be attributed to strong presence of key industry players as well as early adopter customers in sectors like financial services, healthcare and government in countries like the US. Majority of the leading security orchestration vendors such as Palo Alto Networks, IBM, Cisco and Arista Networks have their headquarters located in the U.S., which enables them to cater effectively to the local demand.
Furthermore, regulations around data protection and cybersecurity are most stringent in North America, driving several large enterprises to incorporate advanced orchestration platforms to detect and respond to threats proactively.
Being an economic powerhouse, the region witnesses heavy cross-border data flows and trade activities. This exposes the infrastructure and assets to a wide range and high frequency of attacks. Security orchestration has emerged as a crucial tool for enterprises to gain unified visibility and control over their IT and operational environments spread across multiple locations and jurisdictions.
For instance, in July 2026, Cycurion, Inc. announced a strategic partnership with AgileBlue, an AI-powered Security Operations platform provider. Under the terms of the agreement, Cycurion will serve as an authorized reseller of AgileBlue’s full suite of cybersecurity solutions, including its next-generation Managed Security Information and Event Management (SIEM), Security Orchestration, Automation and Response (SOAR), and Extended Detection and Response (XDR) platforms.
Asia Pacific region has emerged as the fastest growing regional market for security orchestration. Rapid digitization of economies, increasing internet penetration and emergence of digital-first companies drive more reliance on technology in the region. This makes the region an attractive target for hackers and boosts the need for advanced security measures.
Countries like India, China, Japan and Australia have witnessed strong economic growth over the past decade and their governments as well as enterprises are investing heavily in cybersecurity to protect their interests. Many global security vendors have been establishing R&D centers and support offices in Asia to cater to increasing local demand driven by security incidents.
For instance, in July 2024, RSA announced additional strategic investments in the Asia Pacific and Japan region to help support organisations adapt to emerging cybersecurity threats and meet data sovereignty controls and government regulations with the launch of its new Southeast Asia (SEA) Region Cloud tenant, based in Singapore.
Japan’s Security Orchestration, Automation & Response (SOAR) market is growing rapidly, driven by surging cyber threats and strong regulatory pressure. Key trends include increased adoption of cloud-based SOAR solutions, growing demand for managed/security services over pure solutions, and tighter government policy pushing firms to enhance incident response and security posture.
For instance, in May 2023, Swimlane announced further expansion in the Asia-Pacific Japan (APJ) region through the opening of the company’s newest office in Tokyo, Japan, and the general availability of Swimlane Turbine in the region.
The India Security Orchestration market is experiencing significant growth, driven by the rising frequency and complexity of cyber threats across industries. Organizations are increasingly adopting Security Orchestration, Automation, and Response (SOAR) solutions to streamline incident response, reduce manual intervention, and enhance threat detection capabilities.
For instance, in August 2024, Kyndryl announced it has launched a Security Operations Center (SOC) in Bengaluru, India, that offers comprehensive support and advanced protection capabilities for the entire cyber threat lifecycle, using artificial intelligence, specifically machine learning and integrated automation systems.
As organizations scale their security infrastructure and adopt best-of-breed point solutions, orchestration becomes critical to tie disparate products together into a coherent defense system. Compliance mandates and regulations compel companies to automate and streamline incident response procedures.
North America currently dominates the market due to widespread digital transformation and an advanced threat landscape. However, Europe and Asia Pacific are expected to offer lucrative opportunities, owing to increasing government efforts to bolster cybersecurity. Lack of in-house skills required to implement and maintain sophisticated orchestration platforms can hamper the market growth.
Orchestration vendors are focusing on refining risk-based automation, expanding out-of-the-box integrations, and offering cloud-delivered options to boost adoption. As the attack surface multiplies across dispersed IT environments, the ability to detect anomalies, prioritize alerts, and trigger remediation at machine speeds will be critical.
| Report Coverage | Details | ||
|---|---|---|---|
| Base Year: | 2025 | Market Size in 2026: | USD 4.85 Bn |
| Historical Data for: | 2020 To 2024 | Forecast Period: | 2026 To 2033 |
| Forecast Period 2026 to 2033 CAGR: | 15.8% | 2033 Value Projection: | USD 13.55 Bn |
| Geographies covered: |
|
||
| Segments covered: |
|
||
| Companies covered: |
Armis, Attivo Networks, Cisco Systems, Inc., CrowdStrike, D3 Security, Exabeam, FireEye, Inc., Fortinet, IBM Corporation, Microsoft Corporation, Palo Alto Networks, Rapid7, Splunk, Swimlane, and Tines |
||
| Growth Drivers: |
|
||
| Restraints & Challenges: |
|
||
Uncover macros and micros vetted on 75+ parameters: Get instant access to report
*Definition: Global Security Orchestration Market provides solutions that help enterprises detect security threats and coordinate incident response by integrating security products, processes and people into a single system. It allows organizations to automate threat detection, investigation and remediation workflows across security tools and platforms to improve overall security posture and reduce incident response time.
Share
Share
Ankur Rai is a Research Consultant with over 5 years of experience in handling consulting and syndicated reports across diverse sectors. He manages consulting and market research projects centered on go-to-market strategy, opportunity analysis, competitive landscape, and market size estimation and forecasting. He also advises clients on identifying and targeting absolute opportunities to penetrate untapped markets.
Joining thousands of companies around the world committed to making the Excellent Business Solutions.
View All Our Clients